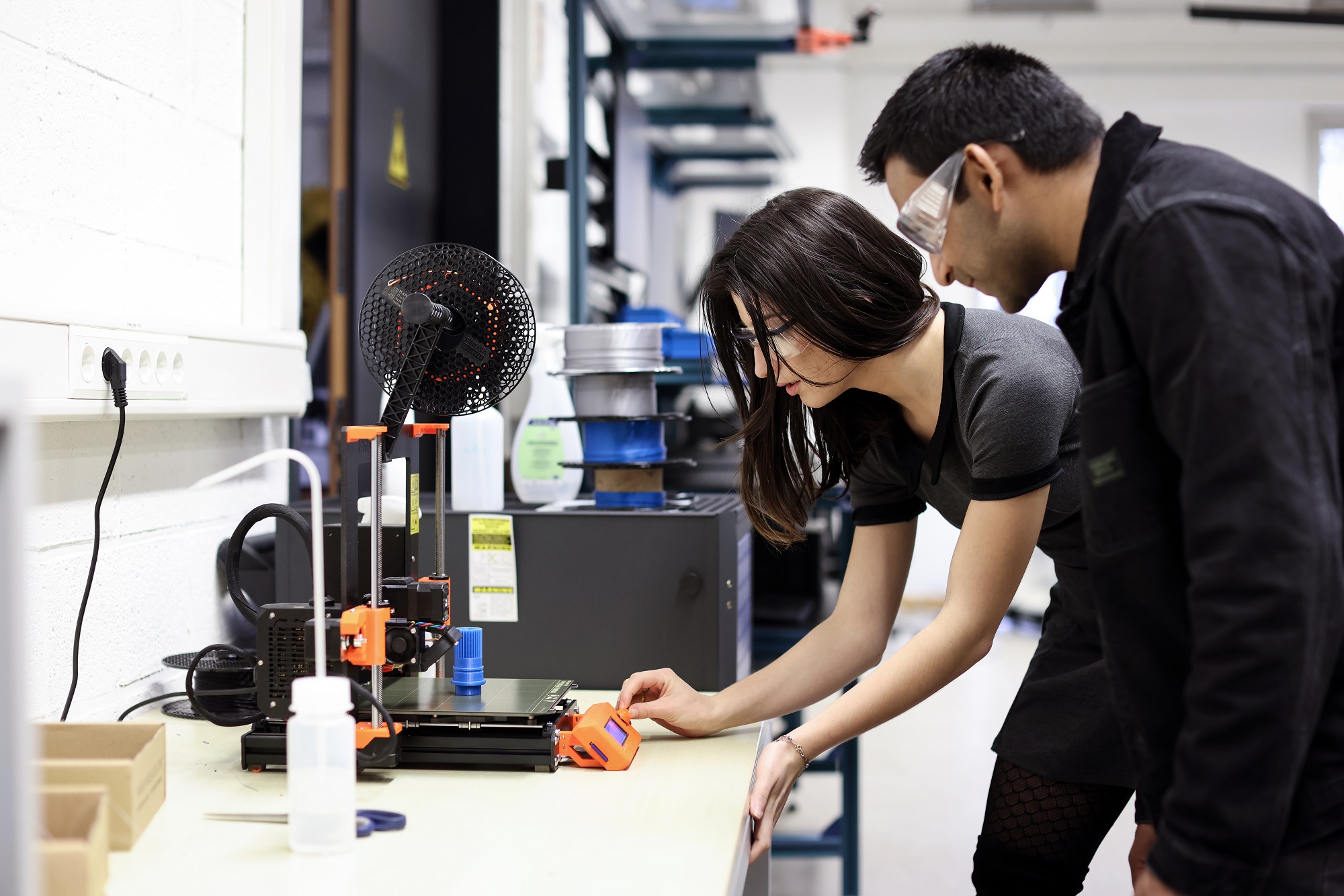
Focus on interdisciplinarity
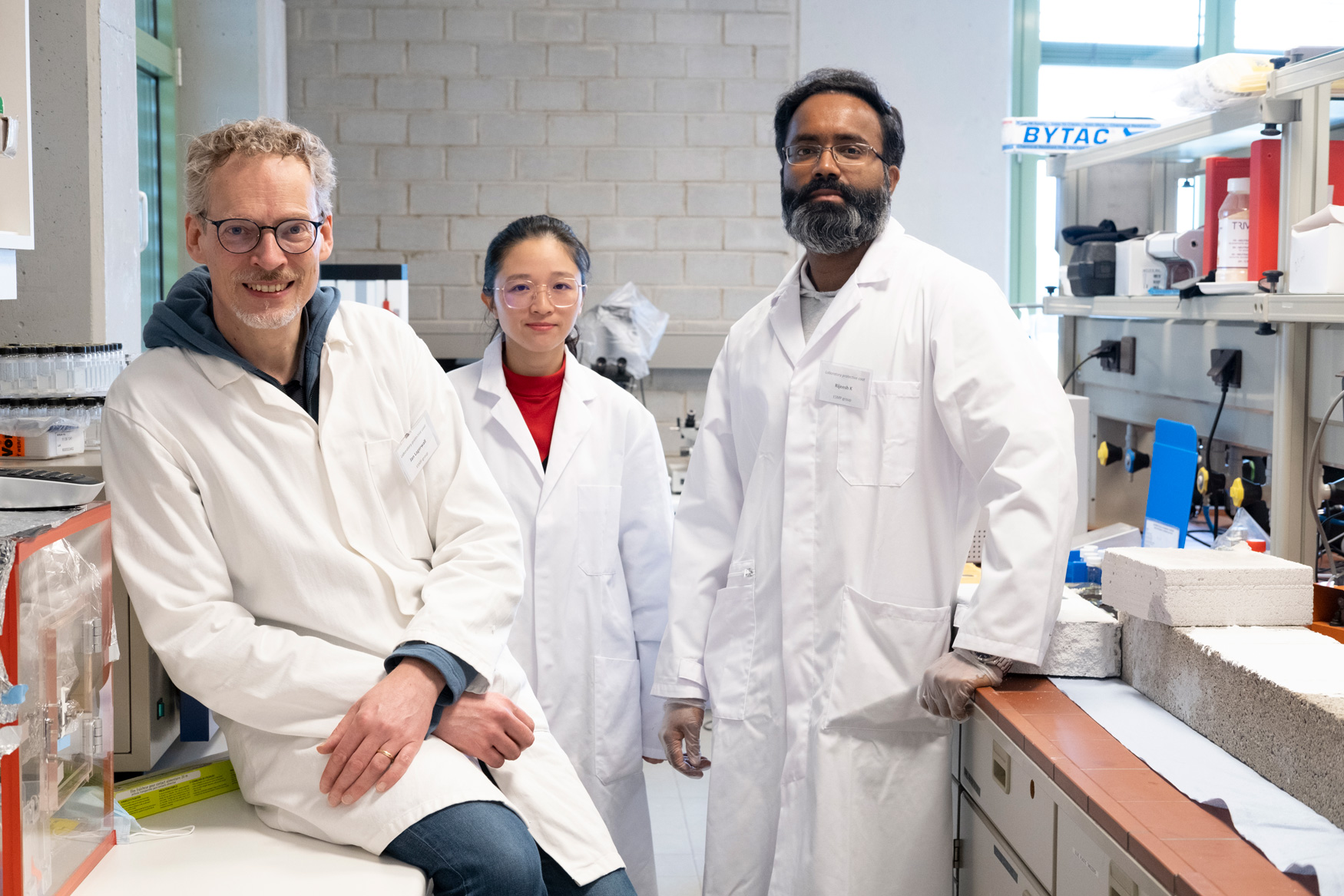
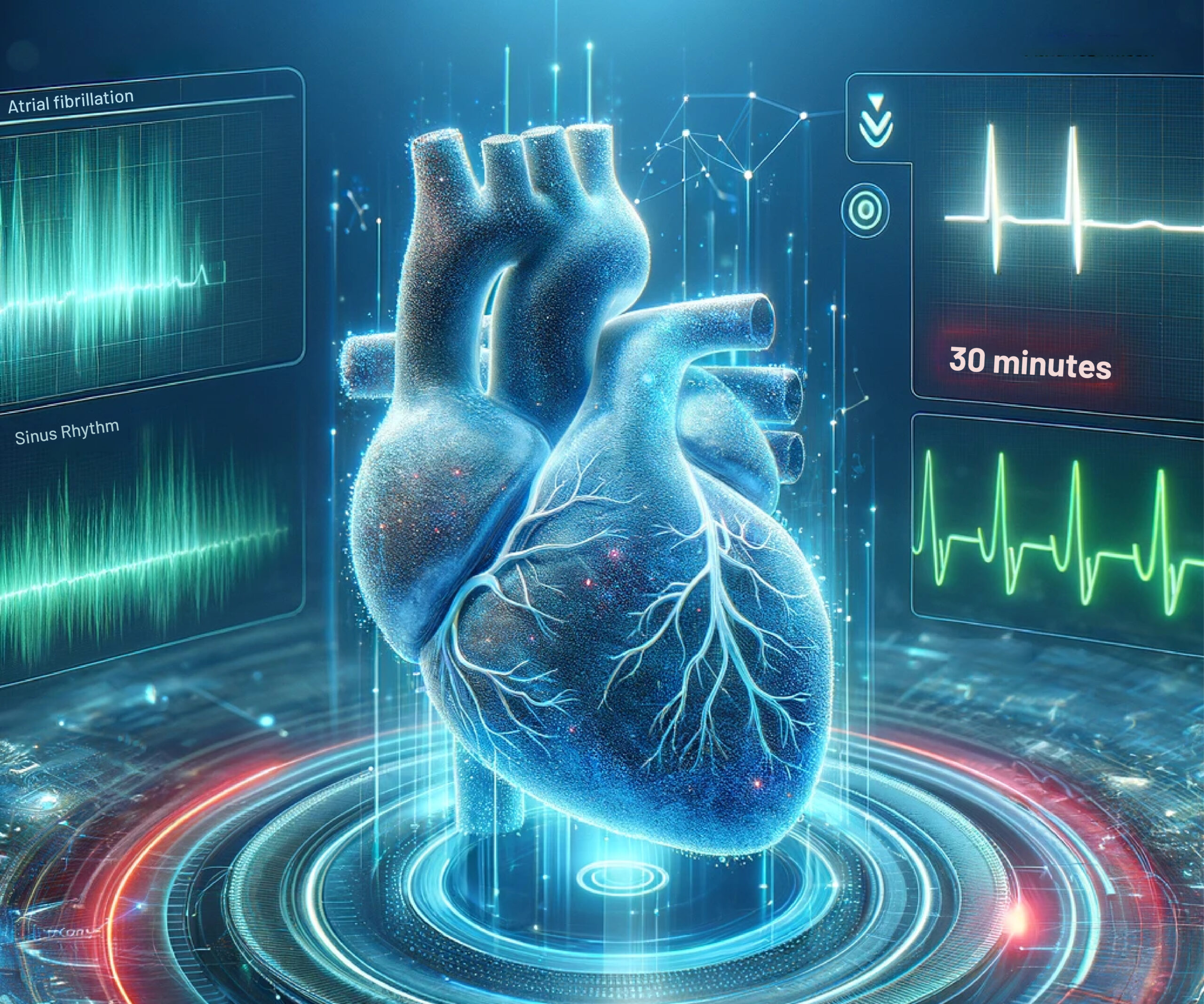
Research news
Our research in numbers
-
1,000+Ongoing projects
-
188Horizon projects accepted
for H2020 and HEU -
20ERC grants since 2014
-
2,440Publications in 2022
We are members of Research Luxembourg
In just a few decades, Luxembourg has successfully built a competitive, innovation-driven research ecosystem. Research Luxembourg is a joint nationwide initiative of the main actors in Luxembourg public research, with the support of the Ministry of Higher Education and Research, including the University of Luxembourg (Uni.lu), Luxembourg Institute of Health (LIH), Luxembourg Institute of Socio-Economic Research (LISER), Luxembourg Institute of Science and Technology (LIST), Luxembourg National Research Fund (FNR), and Luxinnovation.
Reflecting the priority given to research and innovation by the country, it aims to promote scientific cooperation and activities of the research and innovation sector with one ambition: provide the best conditions to make excellence grow and shape a sustainable future.