Discover SnT
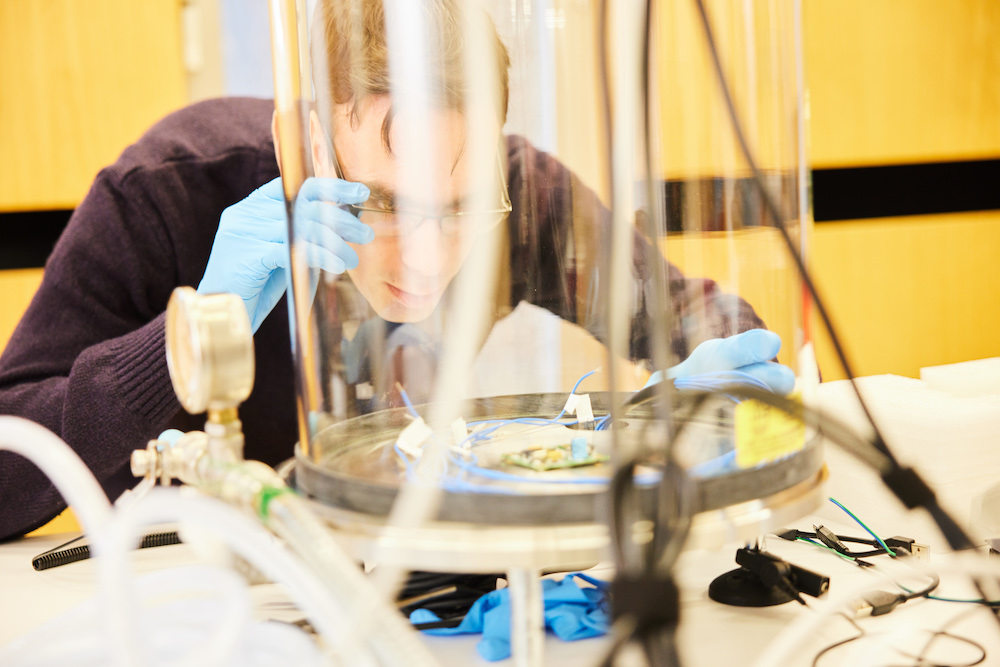
Cutting-edge ICT to Solve
Today’s Challenges
Our interdisciplinary, award-winning research is driven by industry partnerships focusing on four areas: Cybersecurity, FinTech, Internet of Things & Autonomous Vehicles, and Space Systems.
We attract talented scientists and engineers, innovative companies, and leading start-ups from all over the world to develop competitive solutions and create meaningful socio-economic impact.
SnT in Numbers
-
505+Staff
-
18Research Groups
-
6Spin-offs
Our Partners
Launched in 2011, our Partnership Programme was created to support public entities and companies of all sizes to achieve their innovation and optimisation goals, all while providing our researchers with real-world challenges to solve.
Today, our roster has expanded to include 60+ actors from a variety of sectors, including FinTech and space. We work with both public and private organisations in Luxembourg and around the world to ensure our research has socioeconomic impact.
Recent Partners
Latest News
-

Prof. State on ChatGPT and Competitive Advantage
ResearchComputer Science & ICT, FinanceLearn more -